Operation Arachnophobia - Researchers from ThreatConnect and FireEye discovered a cyber espionage campaign originated from Pakistan, targets Indian Government.
ThreatConnect - a new threat analysis company partnered with researchers from FireEye lab to conduct a joint investigation on a series of targeted attacks that could be linked to the Pakistan.
According to the research, Operation Arachnophobia started in early 2013, a custom malware family, first dubbed as Bitterbug that serves as the backdoor to steal information. The researchers say they have not identified the specific victim organizations, they have spotted malware bundled with decoy documents related to Indian issues.
Operation Arachnophobia may be Pakistan’s response to Operation Hangover - a cyber espionage campaigns launched from India. “It was engineered to collect standard Office documents on your desktop,” Barger says. “It was very close to Operation Hangover activity… for which India was purportedly responsible.”
The Bitterbug malware is geared for cyber espionage purposes and was hidden behind a US based virtual private server to make the attacks appear to come from the US. The Pakistani hosting provider appears to have leased its command and control infrastructure from a US VPS provider. “It’s where the malware is hosted and used for command and control,” says Rich Barger, chief intelligence officer at ThreatConnect.
“We know about Russia and China… India and Pakistan has room to grow and mature,” Barger says.
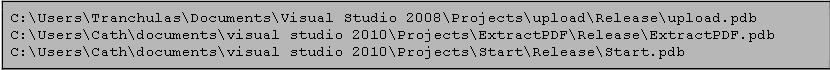
ThreatConnect alleges that the Pakistani security firm Tranchulas is behind as malware samples studied by FireEye researchers. “The ‘Tranchulas’ name was in a string” of the malware, says Mike Oppenheim, principal threat intelligence analyst at FireEye.
How it works:
The BITTERBUG and its new variants uses uses India specific documents and files to infect a computer. This can range from a document on the Khobragade affair to a report on Sarabjit Singh and Indian government circulars.
Once in the system, the BITTERBUG scans for files with extensions like .doc, .ppt, .xls, .pdf, .docx, .pptx, .pps, .xlsx.
A file list containing all documents is then generated. After this a message is sent to the attacker that the computer is compromised. The files are then exported to Islamabad based cyber company.
Conclusion:
Operation Arachnophobia may be launched in response to Operation Hangover for cyber espionage campaign against India. The report can be a speculative in nature as ThreatConnect is a new company and no solid proof are given that any Pakistani company behind this. So, its still a mystery who is behind this. Complete report is available here.