php.net was hacked and exploit kit deployed with five different malware types by the hackers. One malware found by security vendor Seculert, had a unique cloaking property for evading sandboxes. The company called the malware DGA.Changer.
DGA.Changer’s sole purpose was to download other malware onto infected computers, Aviv Raff writes on the company’s blog. Seculert tracked 6,500 compromised computers communicating with the malware’s command and control server. Almost 60 percent were in the United States.
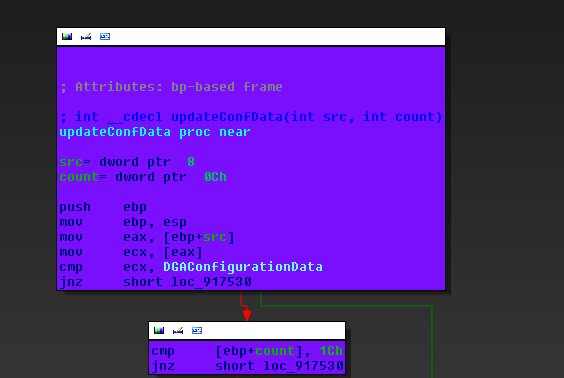
Seculert found that it uses an infinite Domain Generation Algorithm (DGA), but with a twist. the bot can receive a command from the C2 server to actually change the DGA seed. The DGA periodically generates a large number of domain names as potential communication points to the C&C server, thereby making it difficult for researchers and law enforcement to find the right domain and possibly shutdown the botnet.
When the malware generates the same list of domains, it can be detected in the sandbox where security technology will isolate suspicious files. However, changing the algorithm on demand means that the malware won’t be identified.
“This is a new capability that didn’t exist before,” Raff said. “This capability allows the attacker to bypass sandbox technology.”
Seculert found that DGA.Change’s behaviour is not entirely new, exhibiting some conventional and predictable behaviour. After downloading onto a machine, it send OS info, Adobe Flash Info and VM test result back to C2 server.